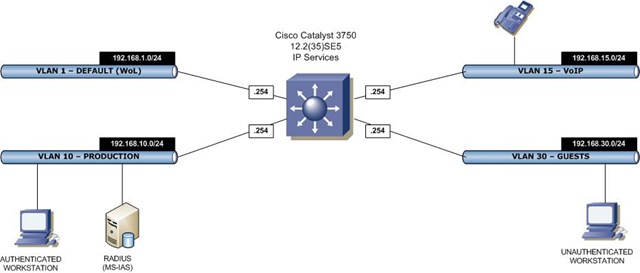
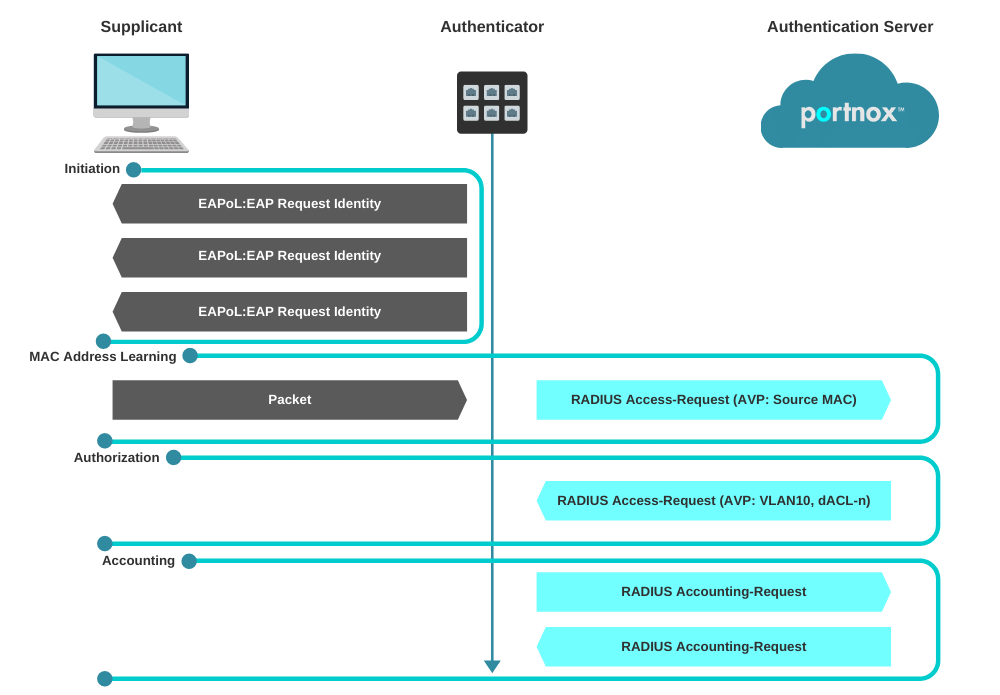
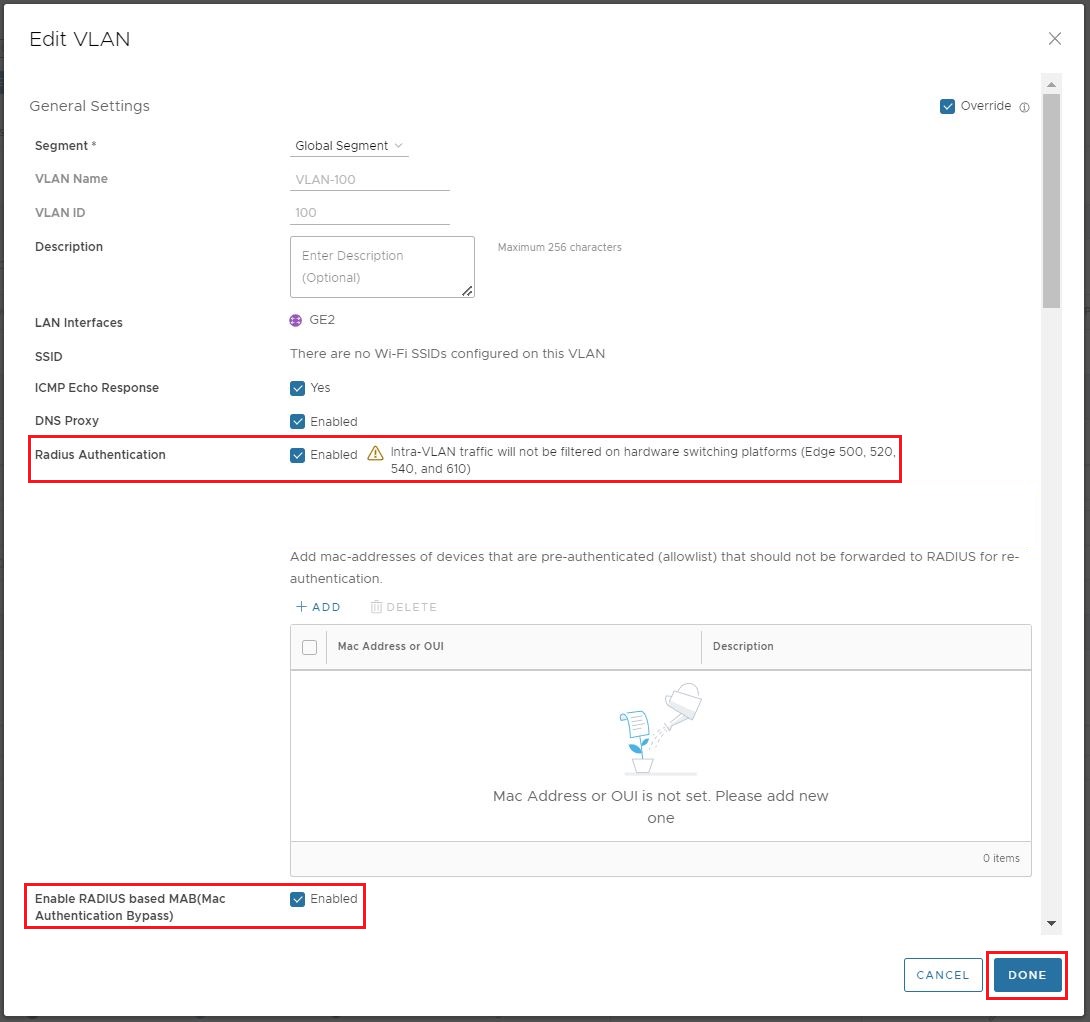
MAC authentication bypass with dynamic VLAN assignment | FortiAuthenticator 6.5.0 | Fortinet Document Library

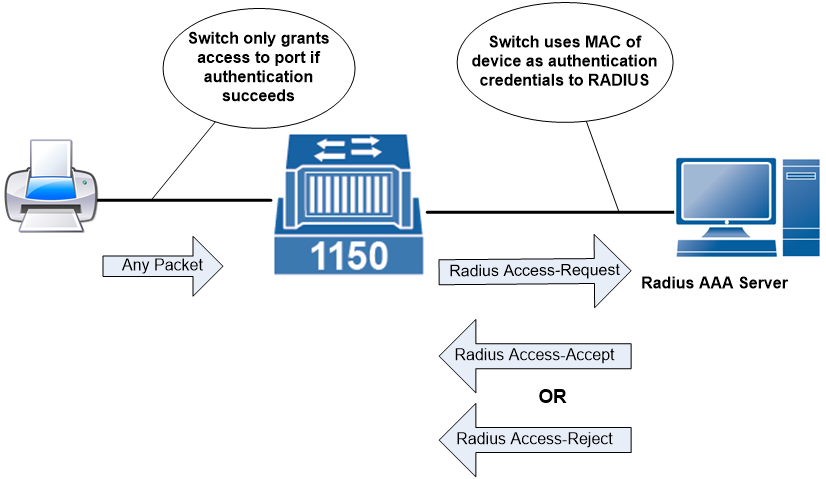
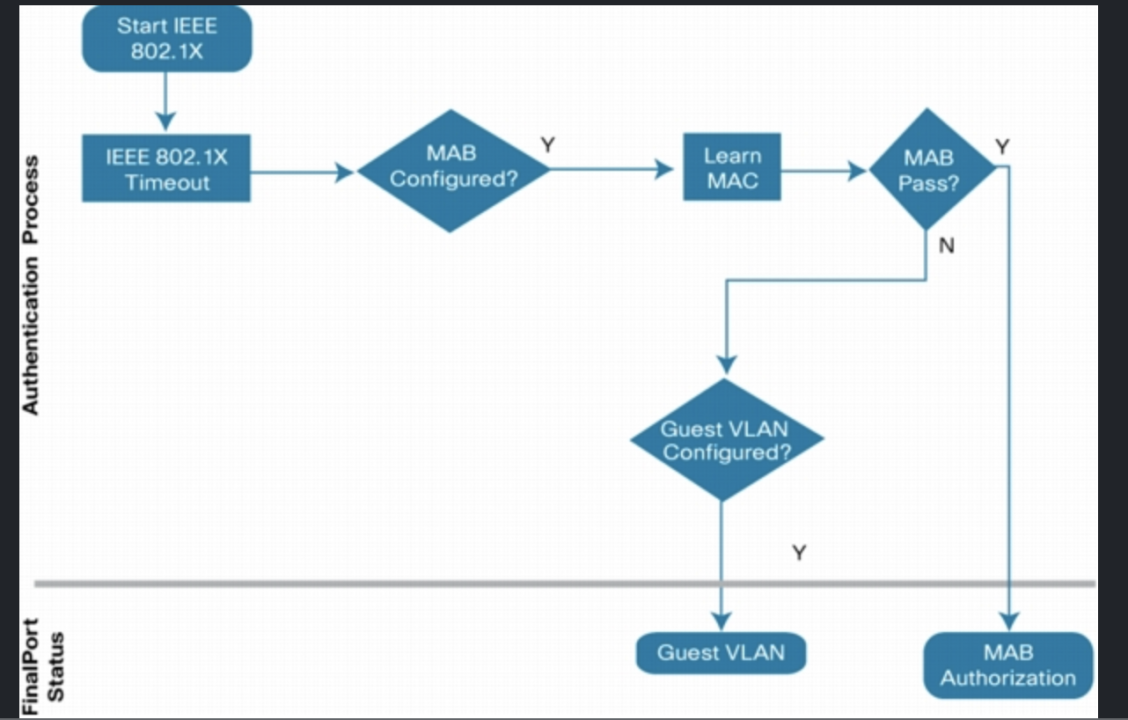
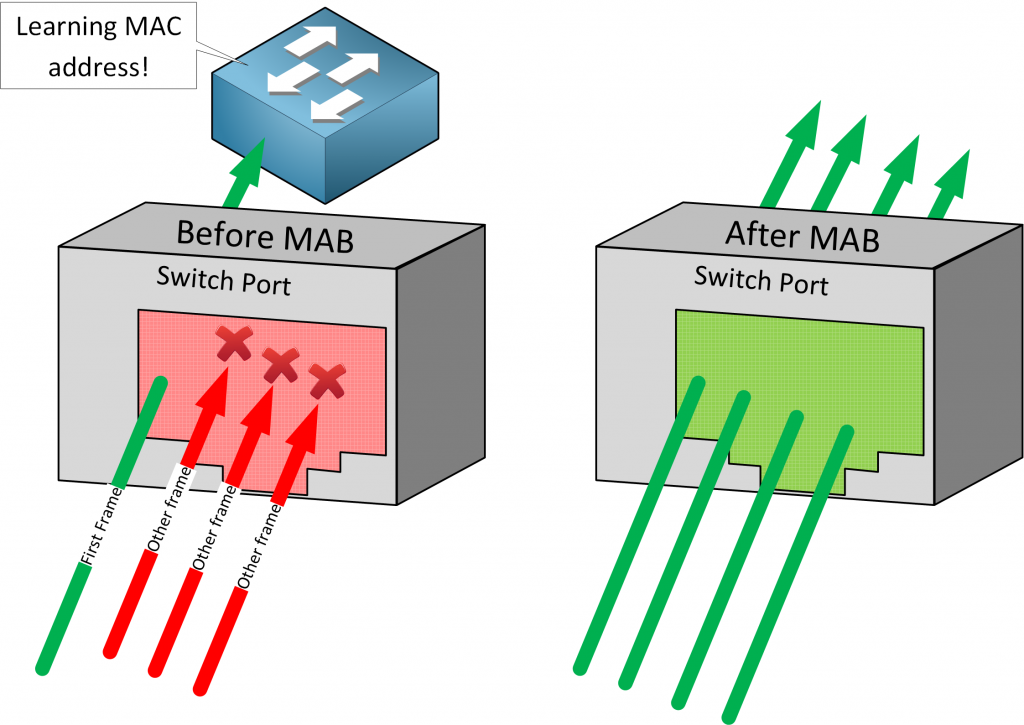
Demonstrates the #MAB ( #MAC Authentication Bypass) rule in #flowchart format #CISCO #ISE #technology #firewall #networking | It network, Cisco, Flow chart